Top 3 Tools That Can Replace Kenna Security
Don’t just replace Vulnerability Management. Upgrade to Vulnerability Exposure Management.
Cisco’s announcement of the end-of-sale for Cisco Vulnerability Management (formerly Kenna Security) creates an important decision point for security leaders: continue on a legacy path or take the opportunity to modernize.
Although the Kenna platform will remain supported until June 30, 2028, support alone does not ensure alignment with evolving customer needs or the rapidly changing threat landscape. Over time, this gap can place security teams and leadership at a disadvantage.
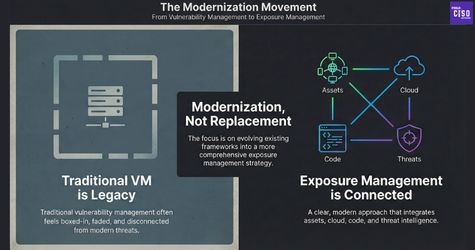
This moment should not be approached as a simple replacement exercise. It is an opportunity to rethink how risk is identified, prioritized, and managed.
Why a Like-for-Like Replacement Falls Short
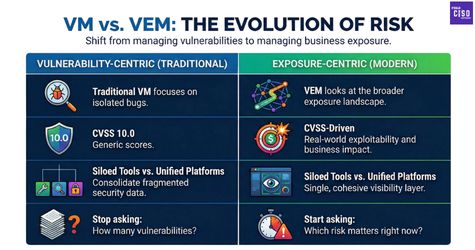
Kenna was designed as a point solution for risk-based vulnerability management. While effective in its time, today’s security environments require broader, platform-based approaches.
Replacing Kenna with another RBVM tool may address the immediate need, but it does not advance the overall security program. True progress comes from moving beyond point solutions to a more integrated and comprehensive model.
What Customers Expect Today
Customer expectations have shifted. Organizations are no longer looking to add tools or complexity. Instead, they are seeking:
- Platform and vendor consolidation
- Simpler, easier-to-use solutions
- Unified visibility across digital environments, from code to cloud
- Risk prioritization based on business impact, threat relevance, and active threat activity
- Integrated workflows that connect discovery, prioritization, validated exposure, and remediation within a single platform
These expectations reflect a clear shift from traditional Vulnerability Management (VM) to Vulnerability Exposure Management (VEM).
Platforms Capable of Replacing Kenna

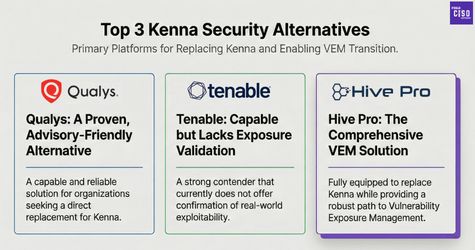
When assessed against these requirements, only three platforms are fully equipped to replace Kenna while enabling a transition to VEM:
All three are capable solutions. However, it is important to note that Tenable does not currently offer exposure validation, which may be a consideration for organizations that require confirmation of real-world exploitability.
The Path Forward
Organizations should not wait until 2028 to take action. A proactive approach involves:
- Transitioning to a unified Vulnerability Exposure Management platform
- Consolidating vulnerability scanning, prioritization, validation, and mitigation
- Reducing operational complexity while improving clarity around risk
Conclusion
The end of Kenna is not a setback. It is an opportunity to modernize.
By moving from isolated vulnerability management to a holistic exposure management approach, security leaders can simplify their technology stack, gain better insight into real risk, and position their organizations for the future.
Did you find this article helpful?
Let the authors know by leaving a like or comment.
No comments yet
Be the first to share your thoughts!