Why the Holiday Season Is a Busy Season in the Cyber World
Cyberattacks don’t spike during holidays because attackers get smarter. They spike because defenders get distracted. The holiday season consistently sees an increase in cyber incidents. This rise is not driven by new attacker techniques, but by predictable shifts in organizational focus, human attention, and operational discipline. As these controls weaken simultaneously, the environment becomes more permissive allowing even basic attacks to succeed at much higher rates.
From a risk standpoint, the holiday season represents a predictable degradation pattern, one that adversaries plan for precisely because organizations repeat the same behaviors every year.
Reduced Staffing and Lower Motivation
During holidays, security and IT teams operate with reduced staffing. On-call coverage is thinner, response times slow down, and vigilance drops due to end-of-year fatigue. A well-known example of how reduced scrutiny during holidays can be exploited is the escape of Carlos Ghosn, who fled Japan during the holiday period by taking advantage of relaxed monitoring and lowered alertness at the airport during security check. Similar conditions apply in cybersecurity: fewer people monitoring systems, slower escalation paths, and a general assumption that major incidents are unlikely during this time.
Security Changes Are Deferred
Policy updates, system hardening, and security improvements are often postponed during the holiday season. Limited staff availability and the risk of disrupting revenue-critical systems lead teams to delay changes. As a result, known weaknesses remain exposed longer than intended, extending the window of opportunity for exploitation.
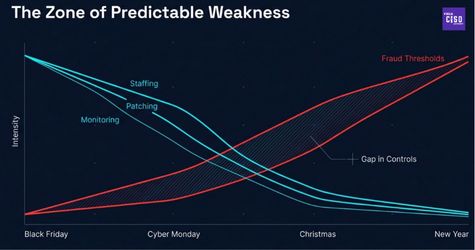
Business Exceptions Lower Security Barriers
To ensure business operations are not slowed during peak shopping periods, organizations often introduce temporary security exceptions. These may include reduced authentication friction, higher tolerance for fraud signals, or relaxed monitoring thresholds. Holiday cyber activity is not evenly distributed across the season. Attacker activity consistently increases around predictable consumer and retail milestones such as Black Friday week, Cyber Monday, and the pre-Christmas rush (December 15–23). These periods combine aggressive promotions, high transaction volume, and reduced tolerance for friction, increasing the likelihood of abuse going unnoticed.

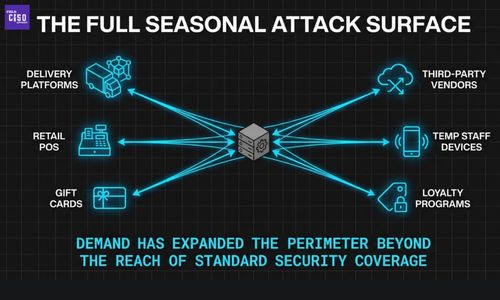
Expansion of the Attack Surface
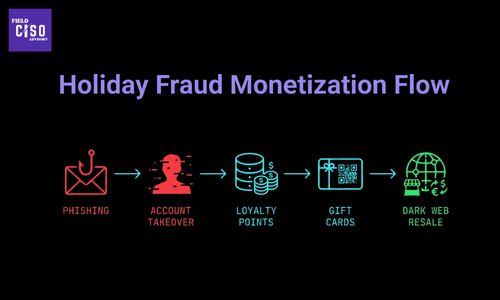
To meet seasonal demand, organizations rapidly introduce new assets such as additional laptops, temporary staff, POS systems, and third-party platforms, often with limited time for security validation. This creates a larger and unevenly protected environment. At the same time, gift cards expand rapidly and become one of the most exploited assets. In 2025 alone, 8.9 million retail gift cards and 7.5 million quick-service restaurant gift cards were observed for sale on underground markets, with some organizations losing up to $100,000 per day as activity peaks around Black Friday and Christmas.
Psychological Factors Increase User Risk
User behavior shifts during the holidays as people become more distracted, emotionally engaged, and pressed for time. Urgency around deals, deliveries, and gifts reduces skepticism and increases impulsive actions. This is reflected in data. During Thanksgiving week 2024, Black Friday–themed phishing increased by 692%, while Christmas-themed phishing rose by 327%, demonstrating how timing and emotional context significantly raise attack success rates.
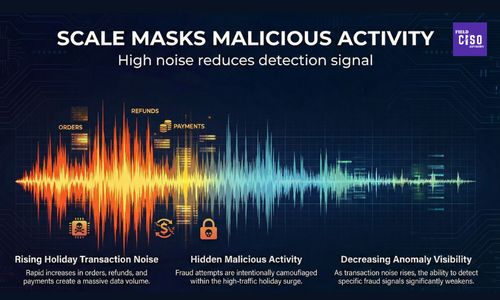
Scale Masks Malicious Activity
Holiday traffic surges create high operational noise. Login attempts, transactions, refunds, and customer complaints rise simultaneously, making abnormal behavior harder to distinguish from legitimate seasonal activity. This delays detection and allows even basic attacks to persist longer. This noise directly enables monetization. SOCRadar’s 2024–2025 Dark Web Monitoring shows that 65% of retail and e-commerce–related posts focus on selling compromised data or access, while 31% involve sharing already compromised information. Between January and October 2025, 311 million stolen accounts were observed on underground markets, with 63% linked to retail brands, providing attackers with the scale needed to exploit holiday conditions efficiently. From a governance perspective, this period exposes gaps in how organizations measure control effectiveness. Staffing ratios, mean-time-to-detect, patch latency, exception volume, and fraud thresholds all drift outside normal tolerances—often without triggering escalation. When key risk indicators are not calibrated for seasonal stress, control degradation becomes invisible until impact occurs.
Conclusion
The holiday season does not introduce new threats. It removes the friction that normally prevents basic attacks from succeeding. Reduced staffing, delayed security changes, business exceptions, and distracted users converge into a single reality: the same attacks work better, faster, and at scale. Organizations that treat holidays as downtime absorb risk unknowingly. Those that plan for them as a predictable stress test of operational discipline are the ones that emerge intact.
Well, Holiday readiness should be treated as a control maturity test, not a seasonal inconvenience.
Did you find this article helpful?
Let the authors know by leaving a like or comment.
No comments yet
Be the first to share your thoughts!