Know your MITRE: Frameworks for simplifying cybersecurity
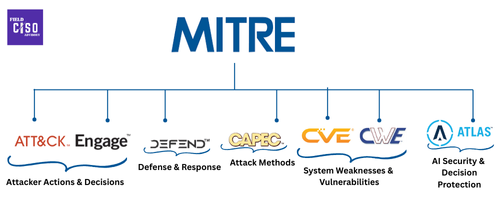
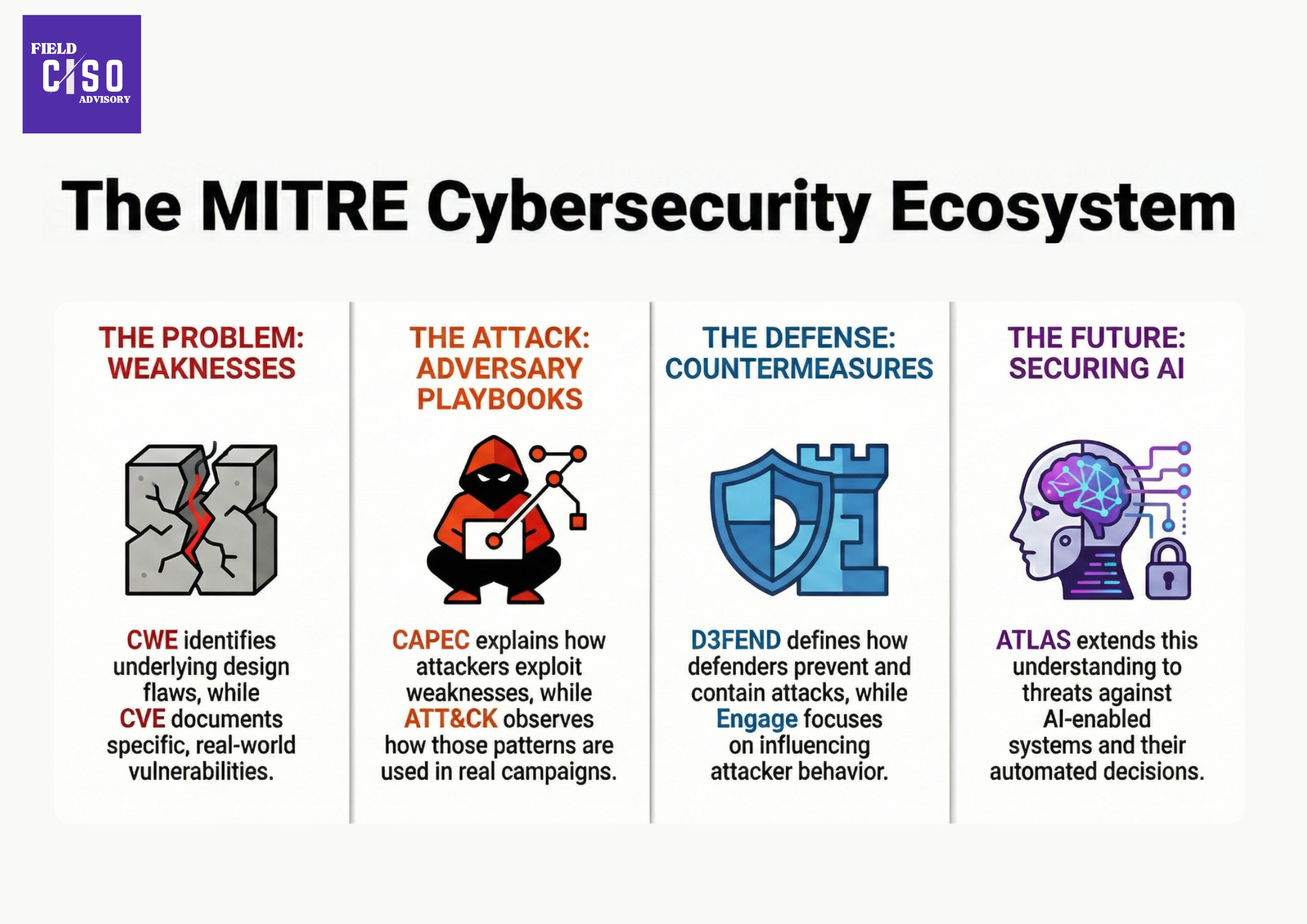
MITRE frameworks are the key components of modern cyber warfare , it describes how an attacker behaves , what controls we should implement , and what disrupts an attacker’s ability to operate.
Well in a battlefield there are attackers and defenders and MITRE Frameworks is a set of tools that help us know about both sides of the war. They help us study how:
- attackers think and operate (MITRE ATT&CK),
- translate that knowledge into defensive controls (MITRE D3FEND),
- understand attack patterns (CAPEC),
- uncover system weaknesses (CWE),
- track real-world exploitable vulnerabilities (CVE),
- proactively engage adversaries to stay ahead (MITRE Engage) and
- secure AI systems against emerging threats (MITRE ATLAS).
Before we go deeper, here’s how the MITRE ecosystem fits together.
MITRE ATT&CK®
MITRE ATT&CK is a battlefield maps globally available knowledge base of real-world attacks that documents tactics (the attacker’s objectives) and techniques (how those objectives are achieved). The best part is that the tactics and techniques in the framework aren't theoretical but based on the attack observations in the real world. It gives defenders a standard language that SOC analysts, red teams, CISOs, and threat hunters can all understand.
In war terms, it maps attacker intent to movement, following the progression from initial access to impact. Indicators change, but behavior repeats.
How to prevent an attack ? curious about the prevention techniques , well you might find the answer to this question in MITRE D3FEND.
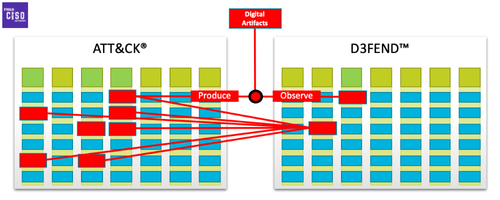
MITRE D3FEND
MITRE D3FEND is a shield used globally for building a countermeasure knowledge base that defines key cybersecurity defense concepts and how they connect.
In a war, defense is not about reacting to every strike , it is about anticipating intent and shaping the battlefield.It structures how defenders prevent, detect, contain, deceive, and recover across the full lifecycle of an attack.
D3FEND is built as a knowledge graph of defensive techniques and their relationships.This graph is mapped one-to-many from attack to defenses.
This is where attacker behavior turns into defensive controls
MITRE CAPEC
The Common Attack Pattern Enumeration and Classification (CAPEC™) is the enemy’s playbook of repeating battle formations, providing a publicly available catalog of attack patterns that show how attacks are constructed step by step to exploit weaknesses.
In war, CAPEC maps these repeatable patterns to reveal how an enemy prefers to fight, helping defenders recognize and act before exploitation occurs.
MITRE CVE
MITRE CVE (Common Vulnerabilities and Exposures) records publicly disclosed cybersecurity vulnerabilities, with one CVE assigned to each confirmed vulnerability by global CVE Program partners.
CVE is a unique identifier for a confirmed vulnerability, allowing vendors, tools, and teams to reference and address the same issue (e.g., CVE-2021-44228 in Apache Log4j).
In war, CVE maps weak points. Once a weakness is confirmed, it is marked and named so commanders know where action is required. It records where exposure exists today.
MITRE CWE
MITRE CWE (Common Weakness Enumeration) represents the weaknesses of a fortress and contains a community-developed list of common software and hardware weaknesses. A “weakness” is a repeatable flaw in design or implementation that creates the conditions for vulnerabilities and attacks. It catalogs failure patterns that recur across products and teams.
In war, CWE maps design failures in defenses that exist quietly until discovered by an enemy, allowing commanders to reinforce the fortress before the first shot is fired.
CWE forms the foundational layer of the MITRE ecosystem by defining the weaknesses that give rise to attack patterns (CAPEC), real-world vulnerabilities (CVE), and exploitable conditions observed in attacker behavior (ATT&CK).
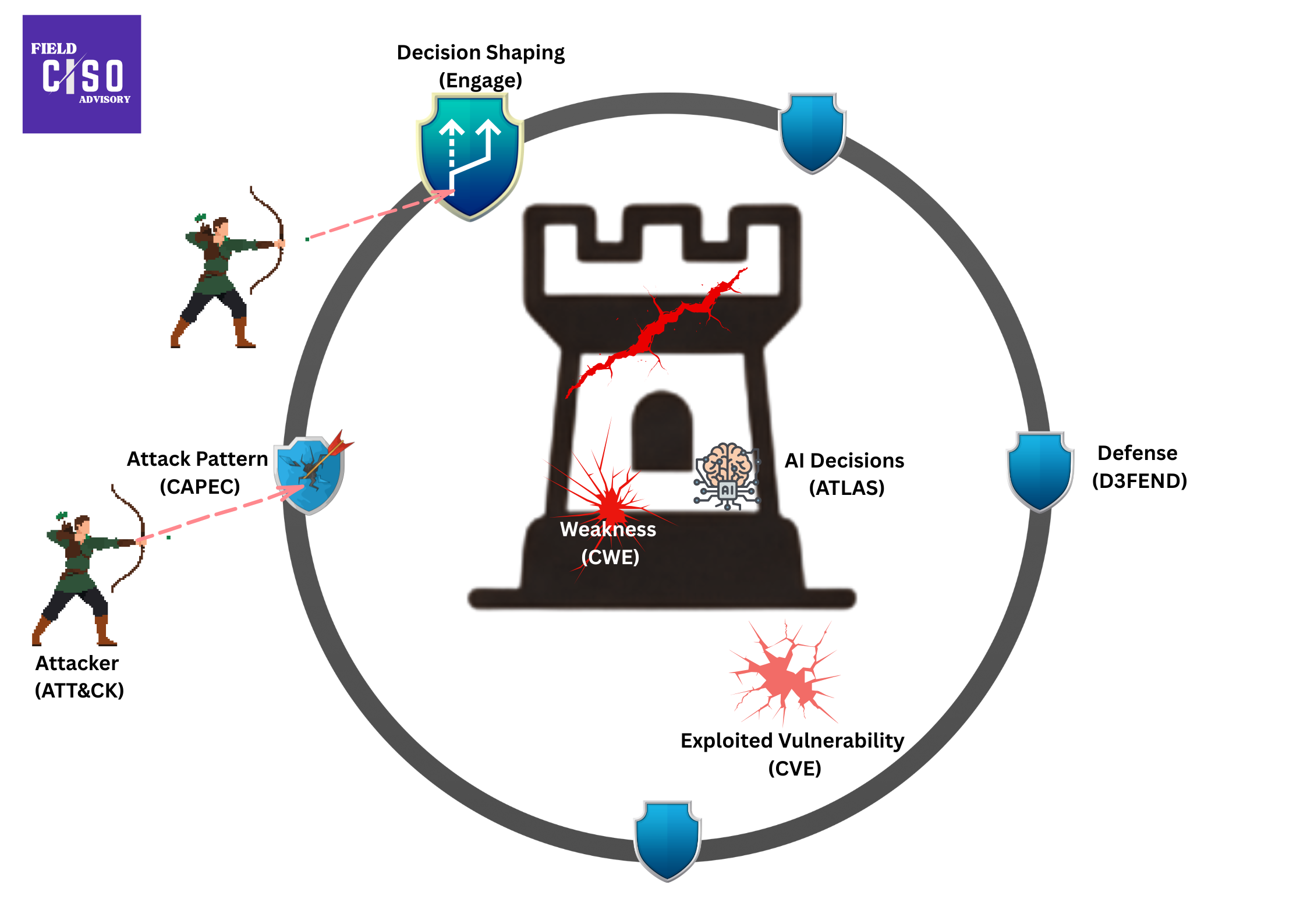
Think of this as the cyber battlefield.
MITRE Engage
MITRE Engage is the art of battlefield shaping that includes planning and discussing adversary engagement operations that empowers you to engage your adversaries and achieve your cybersecurity goals.
In war, MITRE Engage maps how defenders influence enemy decisions through deception, diversion, and controlled interaction, shaping attacker choices before impact.
Engage operates during active attacker interaction before impact, using ethical, controlled engagement to turn interaction into intelligence and delay. Defenders don’t command attackers; they shape the environment by influencing perceived value, risk, ease of progress, and signs of detection.
MITRE ATLAS
MITRE ATLAS (Adversarial Threat Landscape for Artificial-Intelligence Systems) is a globally accessible knowledge base where intelligence itself is the target, documenting real-world adversarial tactics against AI/ML systems and shifting security from protecting systems and data to protecting intelligence across the AI lifecycle.
In war terms, ATLAS maps how attackers target AI decision-making through poisoning, evasion, theft, and manipulation across the AI lifecycle, focusing on behavior and technique rather than just bugs.
MITRE ATLAS shifts security from protecting systems to protecting decisions,showing how AI systems are attacked across their lifecycle and how to protect decision integrity even without traditional alerts.
Cyber warfare is a continuous campaign, and the MITRE frameworks provide its battlefield map across design, exposure, behavior, and response.

Conclusion:
- MITRE CWE identifies underlying design and implementation weaknesses that make systems vulnerable.
- MITRE CVE documents where those weaknesses manifest as confirmed, real-world vulnerabilities.
- MITRE CAPEC explains how attackers systematically exploit weaknesses through repeatable attack patterns.
- MITRE ATT&CK observes how those patterns are executed in real-world intrusion campaigns.
- MITRE D3FEND defines how defenders prevent, detect, contain, and recover from such activity.
- MITRE Engage focuses on influencing attacker behavior during active interaction.
- MITRE ATLAS extends this understanding to AI-enabled systems, where the integrity of automated decisions becomes a primary security concern.
Did you find this article helpful?
Let the authors know by leaving a like or comment.
No comments yet
Be the first to share your thoughts!